CONTACT US

 Please enter your name.
Please enter alphabets only for Name.
Please enter Organization.
Please enter valid email id.
Please enter Phone number.
Please enter numeric only for Phone number.
Please enter your name.
Please enter alphabets only for Name.
Please enter Organization.
Please enter valid email id.
Please enter Phone number.
Please enter numeric only for Phone number.

By Jyoti Bilgoji On 22 May 2019
The zero-trust network model implies limiting access to a company’s intellectual and sensitive data and strictly giving access to only those who absolutely need it. As traditional security infrastructure/methods are proving to be ineffective against sophisticated data breaches, the idea behind a zero-trust model (ZTM) is that anything and everything, either inside or outside of the network boundary, cannot be trusted without proper verification.
There are many security controls which are designed specifically to protect internet connections, but there are multiple entry points that can be used to launch a cyber-attack, such as VOIP systems, Wi-Fi, cloud, and WAN, among others, which are not inspected or controlled.
Many security/technical experts are of the opinion that the approach is difficult for preventing attackers from moving without being detected inside a network for high-value targets after they have breached the network boundary. Many recent data breaches have occurred because conventional security controls and data loss prevention tools were unable to catch the culprits who may have used fake/abstract credentials.
The growing number of remote users and the increasing use of cloud services to host various applications and services have also made it difficult for many organizations to establish and enforce a network perimeter. In a zero-trust network, no one can be trusted. We, as an enterprise, must focus on the packets traversing over the network and all incoming and outgoing traffic should be closely monitored.
Zero Trust Security Models comprise of the following pillars:
Verify the user: Passwords alone are not enough to verify the legitimate identity of a user requesting access. The best way to think about enforcing additional factors of authentication is to consider that every access attempt is secured by at least two different types of factors. For instance, it could be:
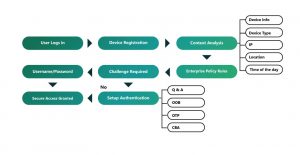
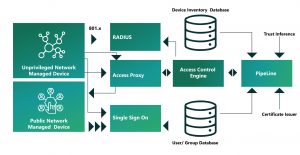
Validate the device: If a user is requesting access from a known, managed, and registered device that they use daily, you can have a certain level of confidence that the request is legitimate, especially if you have also verified the user.
Some of the additional capabilities that a device management solution provides include:
Limit access and privilege: After a user has been granted access to a resource, the user’s privileges must be tightly managed. Personnel with administrative privilege are frequently targeted to exploit network vulnerabilities and gain control over business systems. With zero trust security, it is important to limit lateral movement within all resources such as applications, servers, or workstations by limiting users to only the access they need to perform their jobs.
Employing a zero-trust network can be challenging. Along the way, the company must redefine and streamline job roles, responsibilities and data classifications, to build an entirely new service for keeping track of devices, enable improved visibility over its applications and overall user authentication as well as access control policies.
A key aspect to keep in our mind when transitioning to a zero-trust network is that nobody can have access to internal resources until it is verified by a trusted party.
The user should be given access based on what we know about the user, and what we know about the device being accessed from our enterprise application from inside the network boundary or from outside.
We should focus mainly on securely authenticating all users, have up-to-date knowledge of roles and responsibilities and have the ability to instantly recognize abnormal user activity/ device behavior with latest technology called user and entity behavior analytics (UEBA). Our motto with the zero-level trust is to move to a model in which verification is a must.
When we are planning for zero trust network, it is important to design security from the inside-out and not the other way, Businesses need to be concerned about the attack surface and focus mainly on the protecting surface network.
To protect sensitive/critical data, we should know where it is stored, how the data flows in the entire enterprise, who are the regular users, and who has access to it. Many organizations say that if you cannot trust the network to provide secure access to company assets and intellectual property, then you must have current data about the users and machines accessing them.
To enable zero trust, stringent methods for securely authenticating and identifying users/devise, is an imperative. The company’s resources should also be fully authorized, fully encrypted and authenticated based upon the state of the devices as well as user credentials.
No related posts.
Jyoti is a former Happiest Mind and this content was created and published during her tenure.
Jyoti Bilgoji Jyoti is a former Happiest Mind and this content was created and published during her tenure.
Read other blogs by Jyoti Bilgoji
These blogs might interest you

by Surenthar M on 22 Apr 2024
by Hariprasad C.R. Rao on 18 Apr 2024
by Vivek Manu on 15 Apr 2024
by Vinod Kumar on 12 Apr 2024
Tag Cloud
Subscribe for blog updates
Technology Focus
News & Events
RESOURCE CENTER
ABOUT HAPPIEST MINDS
Happiest Minds enables Digital Transformation for enterprises and technology providers by delivering seamless customer experience, business efficiency and actionable insights through an integrated set of disruptive technologies: big data analytics, internet of things, mobility, cloud, security, unified communications, etc...
© Happiest Minds 2024 Terms and Conditions Privacy Policy







