With clinics and hospitals adopting digital systems more than ever before, patient identity and medical records are susceptible to cyberattacks. Healthcare data and patient privacy face threats since ePHI (electronic protected health information) is vulnerable to cyberattacks in the digital world. The rapid adoption of remote and telehealth (IoMT) has improved healthcare quality, affordability, and accessibility, yet it remains susceptible to data breaches and cyberattacks.
Patient information is a gold mind on the internet. Several breaches for misuse of data have been reported, which make the healthcare sector accountable and responsible for the protection of its databases, networks, and endpoints. This makes an impenetrable cyber defense strategy critical for healthcare providers. Medical practitioners need to remotely access medical data, which makes the healthcare business vulnerable to attacks.
The Top Healthcare IT cyber security challenges are:
- Many healthcare institutions continue to use outdated technology that impacts productivity and leads to treatment mismanagement.
- Adequate security controls are often lacking in medical devices.
- Healthcare workers lack cyber risk training.
- Systems connected to the internet like ventilators, vital sign monitors, X-ray machines, CT scanners, MRIs, and patient tracking wristbands can be easily exploited or tampered with.
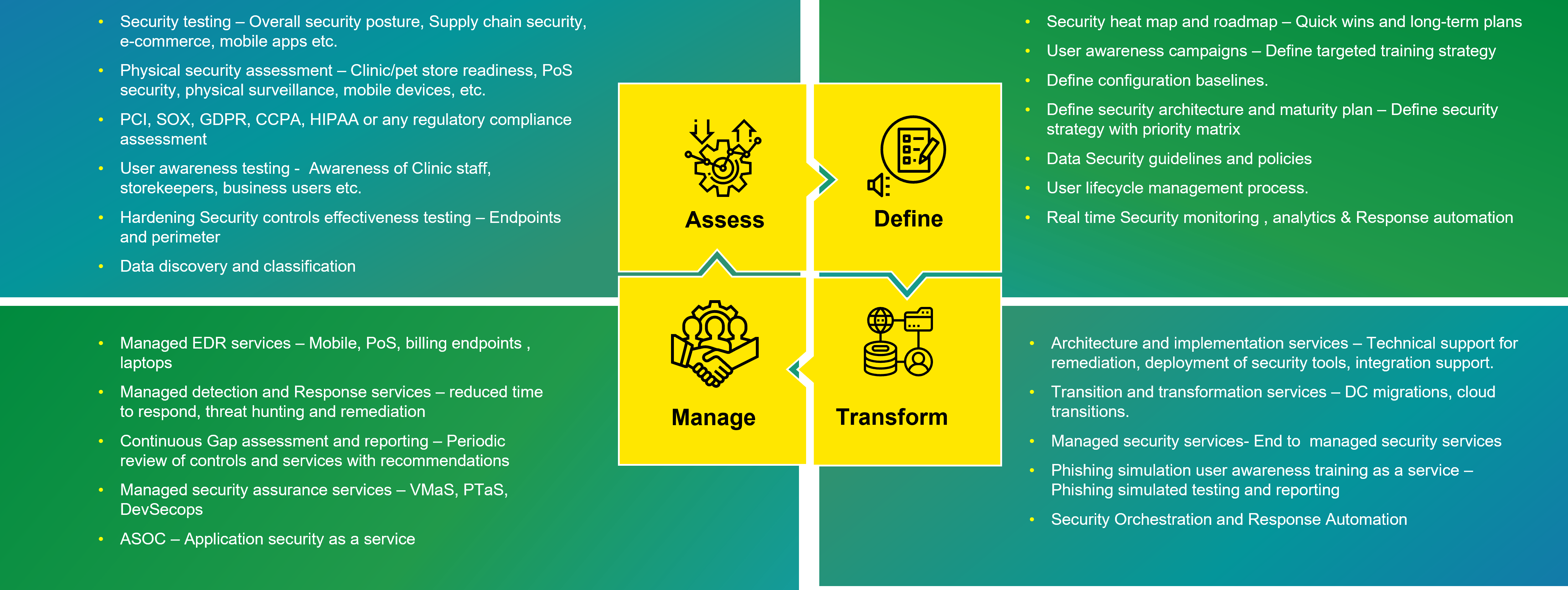
Our Services:
Happiest Minds enables end-to-end security for the Healthcare business by applying a robust and proven framework built in accordance with regulatory requirements, digital security best practices, and best-of-the-breed tools and technologies. We help you stay updated with evolving governance policies to improve and tighten healthcare security in the following ways:
- Our security architecture and design aim to build and manage a resilient healthcare system with leading AI/Big Data/behavioral-based analytics and periodic compliance assessments, reviews, and management.
- We ensure that your organization is HIPAA/HITRUST ready so you can meet regulatory compliances.
- A centralized management and monitoring framework provides medical devices, endpoint, network, and data security, powered by best security practices, knowledge, and experience.
- Support your digital transformation initiatives leveraging secure cloud adoption and medical device security.
Our Solution – 360° Approach