An abstract definition of Information Security is- Building defense mechanisms to protect three key assets of an enterprise
1. People
2. Process
3. Technology/Digital
Adherence to specifics of process definitions as laid by the external directive body is referred to as ‘Compliance’, in other words:
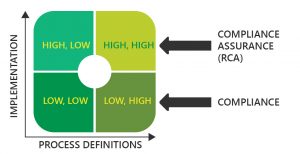
Compliance, as a domain of InfoSec checks for the existence of adequate processes and not its implementation.
Banking, Financial Services and Insurance (BFSI) being highly regulated segment has maximum external directives by applicable regulators & international standards.
What is RCA?
Regulatory Compliance Assurance (RCA) is an assurance program built on Happiest Minds customized Information Risk Management (IRM) framework built to consolidate the requirements of International Standards – ISO 27001, PCI DSS International best practices- CIS, NIST and cybersecurity guideline requirements of domestic BFSI regulatory – IRDAI, RBI & SEBI.
RCA Drivers
- International standards and best practices existed before regulatory requirements for cybersecurity.
- With discrete management systems, organizations’ not able to realize the value of different standards.
- RCA consolidates international standards and best practices under a single management umbrella to help organizations realize cross standard benefits.
- RCA focusses on implementation and process definitions, unlike other compliance programs focusing on only process definitions.
- Lack of checks on the effective technical implementation of the defined processes.
Program uniqueness:
- Delivery Model: Onsite or offshore.
- Program inclusions:
- RBI, IRDAI & SEBI mapping with ISO 27001 & PCI-DSS.
- Data privacy requirements of guidelines of AADHAR (UIDAI), Personal Data Protection bill 2018 and IT Act.
- IRM/DRM framework using the above applicable guidelines and digital security standards from CIS & NIST.
- Assurance program covering consulting to control deployment to periodic compliance assessments.